First of all is why random password?
Traditionally, I only use random password on really important website when I really need a super strong password. On most cases I use easy to remember password. I have a small pool of passwords that are strong but also easy to remember for me, I use those passwords on many sites.
But then the news of some massive data breach at may top sites panic me. Even top site like Linkedin, Dropbox, etc have suffered from data breach. This make the password I use on those website at risk. Even thought these site are well designed and stored my password in hash encryption. People will eventually brute-force their way through those hashing algorithm and that put many sites which share the same password at risk. So I was left with no other choice than to change password of any website I have used.
Therefore I decided to use randomly generate password now on. This have two advantage:One, I will have a strong password for every site, not necessary in some cases but it doesn’t hurt either. Two, I will have unique password for each website so in case one of them got data breach, the damage is contained. In order to do that, I will require two things: An easy to use, and quick to access password generator and A browser that can save password and sync them among devices.
About the password generator
You can find password generator anywhere on the web nowadays. However I need something simple, lightweight and no nonsense. So a little googling around show me pwmake, which belongs to libpwquality, a dependency of cryptsetup, gnome-disk-utility:
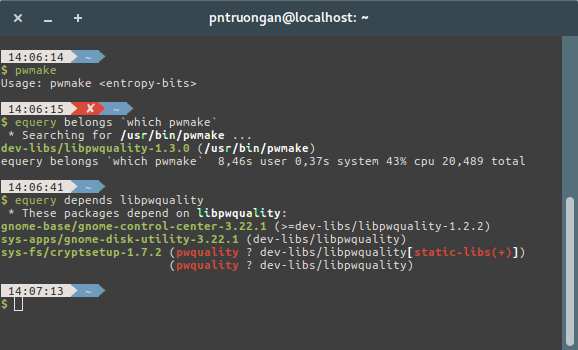
So If you have ubuntu or any gnome installation, chances are you already have pwmake and no installation is require, which is great. The only argument pwmake require is the number of entropy bits it will take. Normally the number of entropy bits only matter if you’re generating tons of password at the same time. Those bit will make sure those tons of password are truly random and doesn’t form a pattern. But since I only generate 1 password at a time. Any amount of entropy bits would do, even zero is good.
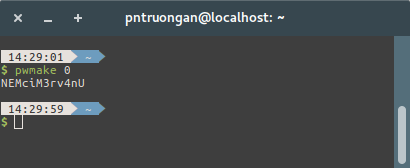
Since I always have a terminal window hovering in the corner, poping it up, type that command quickly and copy the generated password is no hassle. Genrated password is always 8 characters or more, with lower case letters, upper case letters and number or symbol mixed in. That’s good enough for most website. If I need longer password, I can throw in more entropy bits.
And for the password manager.
When you use randomly generated password, you won’t be able remember to them. There’s no way that you can remember a set of long, randomly generated, case sensitive strings with symbols and numbers mixed into them, it’s just impossible. Even if you remember them, typing them is a real pain and typing them on all the devices you own, like a smartphone, it’s extremely painful. Luckily every major browser nowadays can remember password, autofill them when needed and sync them across devices. It’s god sent relief.
Now there would be some a lot of dedicated password manager software there but at time goes by, browser’s built-in password manager is the best choice in my opinion. First, the stand alone password manager is not well integrated, they may not autofill the password correctly. In most cases you will end up having to install a browser extension just so the stand alone pass manager can work. Second, stand alone may not be available on all your platform and devices, browser like firefox for chrome is very well supported on almost all platform. And the builtin password manager has grown a lot nowadays.
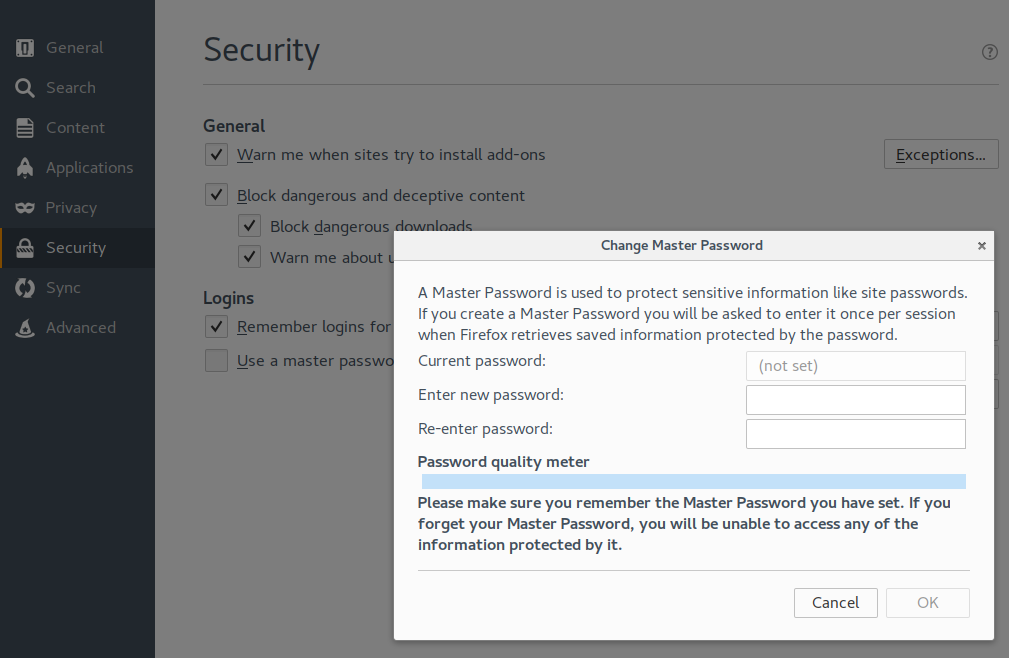
To start using the browser password manager just press save password whenever your suppose ask you to, it’s simple as that. If you need more security consider setting a master password, more on that later.
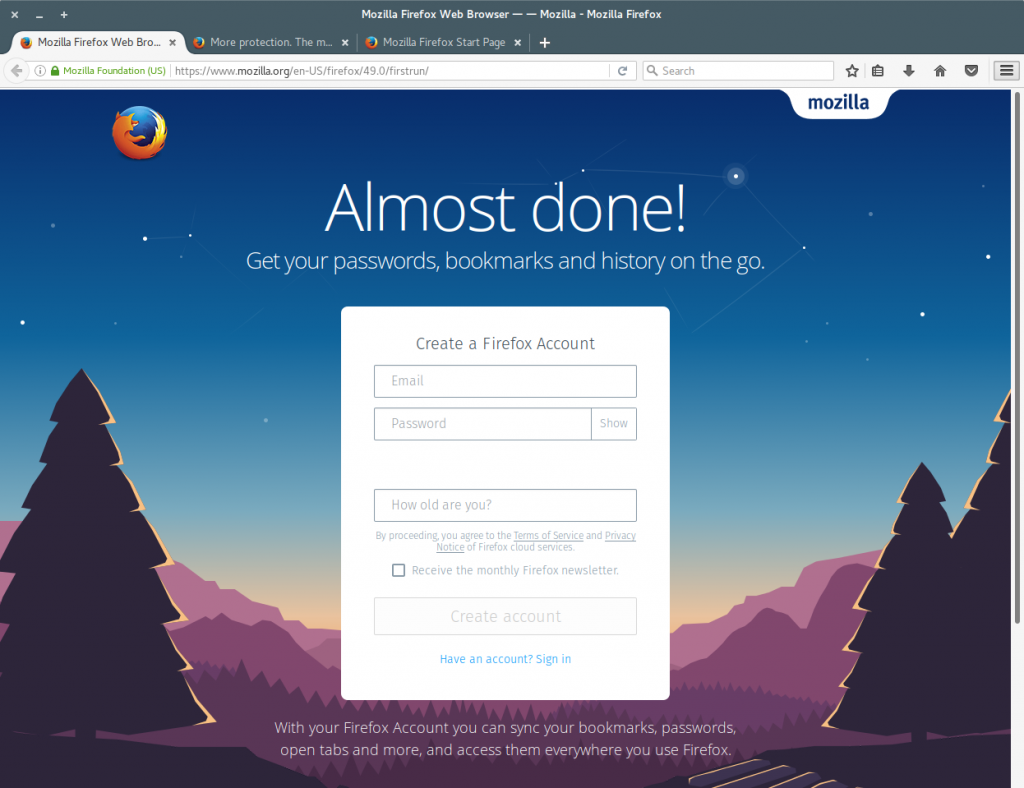
And finally, either firefox or chrome support password syncing over all of your devices. All you need is an email, when you start firefox for the first time you will be prompted to create a firefox account. If you missed this screen, you can access it again via the sign-in to sync option
An interesting thing I notice as a long time firefox user is that firefox have to password syncing mechanism: https://blog.mozilla.org/services/2014/04/30/firefox-syncs-new-security-model/
Ideally one won’t want his/hers password to be store in plain sight on some server, a data breaching in that server would be disastrous. So all password syncing service encrypt the password before sending them to server, which is fair enough consider that modern encryption algorithm is pretty strong. However, when those encrypted password is transfer from the syncing server to your new devices, they will require a decryption key.
Now, it would be easier for users if the Firefox account password was also the decryption key. That way when you login to download your synced information, you can also decrypt it without a need for additional password. But that would mean if your firefox account password was compromised, people can get all of your password in one place, JACKPOT. So in the early days, firefox want to ensure the maximum security by separatint the account password and the decryption key. Instead, after you login from a new device, you can download the synced information but cannot read it. You will have to do the pairing, a special operation that allow one of your old device to securely transfer the decryption key to your new device. And this pairing process is HIDEOUS. So they later change their mind and went back to the normal way.
As for the master password. It’s meant to protect your data in case someone on got a hold of your device. Now I won’t worry much about data safety when my device got stolen, I have full disk encryption for that. The problem is when someone ask to use your device and you can’t refuse. When you set the master password, browser will encrypt all of your sensitive information. The master password is not saved on your computer, browser will ask you when it need access your data and remember this password for one session only. If someone ask to borrow device, you can simply quit your browser, easy like that.